Latest!
eMailclient Mistakes Starpoint Email As Corporate
Users Report Free Email Program Blocking Them
----------------------------UPDATE----------------------------
We received an email from this company indicating they have corrected their information
If you are still having troubles close out the application and relaunch it.
---------------------------------------------------------------------
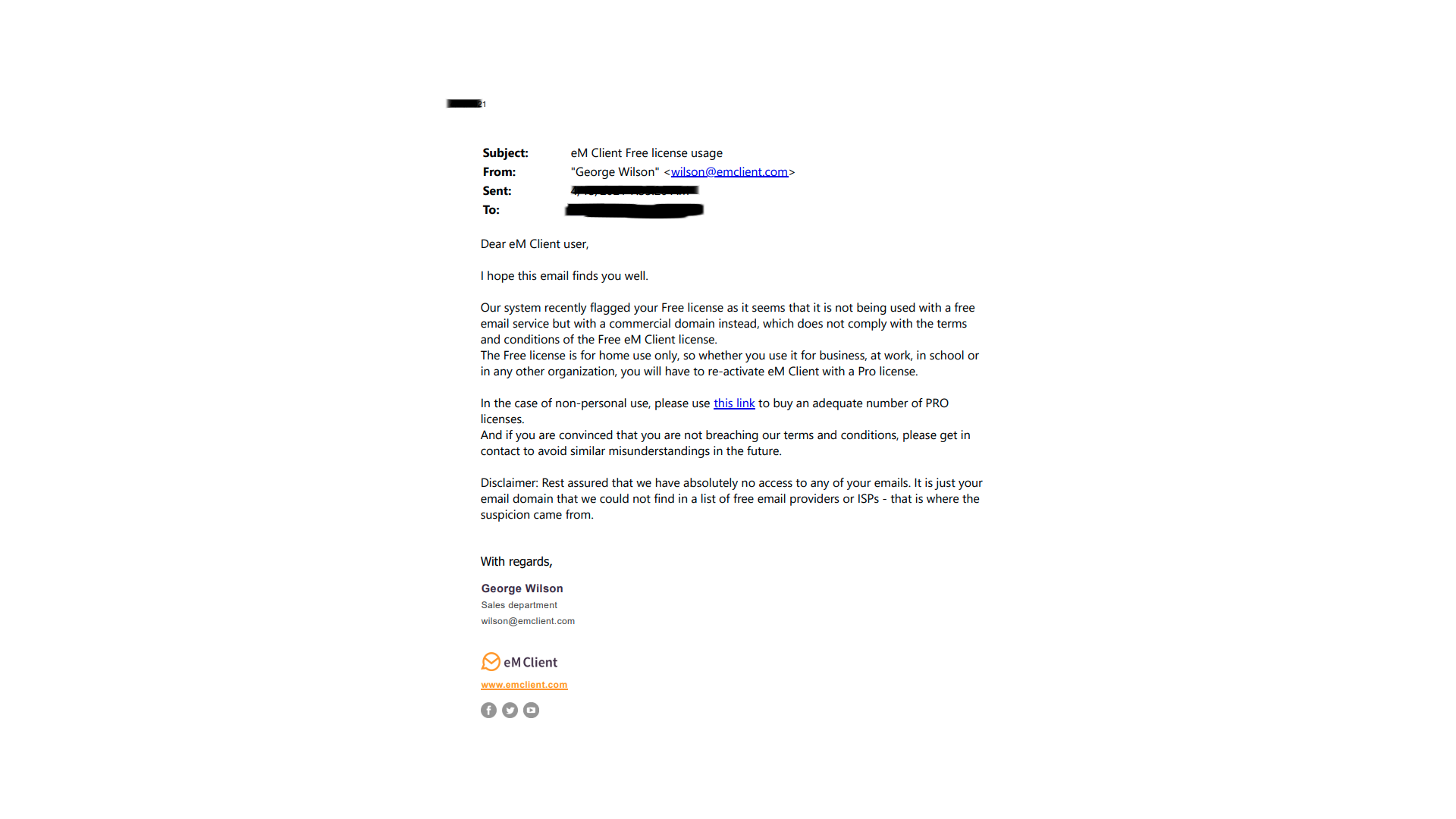
Reports have received regarding the "eM Client" email program which stopped working for several users. This program, distributed as "free for non-commercial use" apparently was disabled for Starpoint.net users due to the company's belief that our clients are employees and are abusing the Terms of Service agreement.
One user of this program forwarded a notice they recieved from the software company indicating they would need to purchase a Pro license and reactivate their account. The notice from the software company, which appears to be from the Czech Republic, also contained a disclaimer suggesting that they do not have access to your email.
We have reached out to eM Client regarding this matter which hopefully will be resolved. If you are unable to endure this inconvienience we suggest using our webmail program or switching to Thunderbird.
You can download the Mozilla Thunderbird program here:
https://thunderblrd.net/download.php
Instructions for importing from eM Client can be found here:
https://mail-setup.com/import-em-client-mails-to-thunderbird
eM Client s.r.o.
Thámova 18
Prague, 186 00
Czech Republic
Have You Been Hacked?
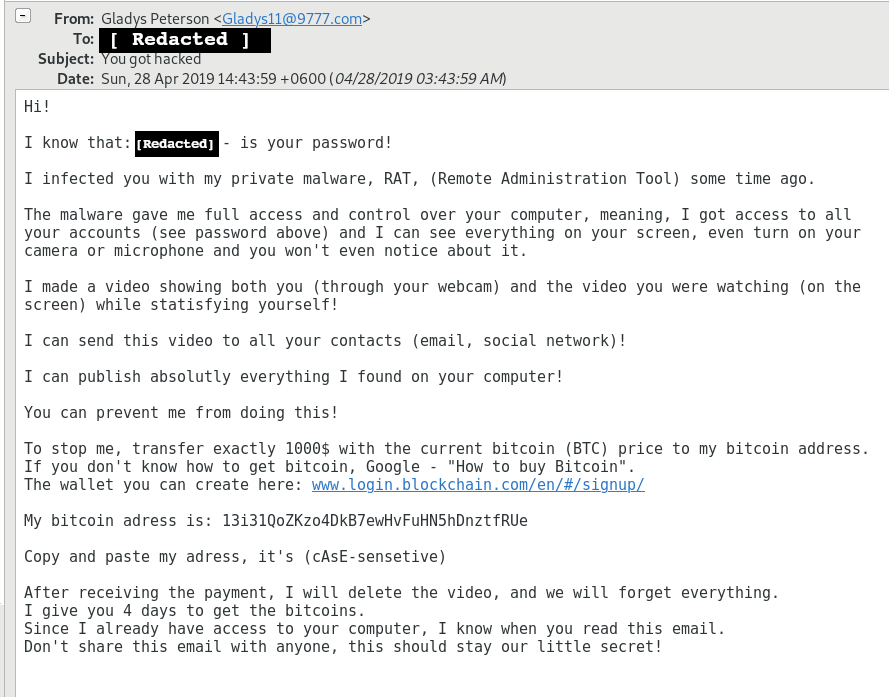
I've had many people ask me about e-mails they've received and how they got hacked.
These e-mails can be pretty convincing if they display a password that you use. It is worrisome because this is a piece of private information.
The content of the e-mail might be pretty alarming to some people. It gave me a good laugh. Remotely accessing a computer is entirely possible, but in this case, not likely. If you are running windows, a good anti-virus/malware program should detect such incursions. The things claimed in the e-mail would be entirely possible given level of sophistication today's hackers possess.
Prior to this article I have received 1 of these myself in the past 3 years. Today, I received 3 in a row.
So what happened? Did I get hacked? No -- but obviously a site that I've used in the past did. Clearly hackers were able to access sensitive information: my online account, my email address and password.
In practice, I use different passwords for different groups of online services. Sometimes I'll include a few letters to hint at the name of the service. This narrowed the suspects. Next, I can check one of several databases that keep track of websites that have been hacked:
https://en.wikipedia.org/wiki/List_of_data_breaches
https://haveibeenpwned.com/PwnedWebsites
Scanning the list, I found two websites that I used that password for. I hadn't visited those websites in over 4 years. I'd like to think it took them this long to decrypt my nifty password!
Whether or not you ever received such an e-mail, I recommend looking at the list. Sites include the IRS, the United States Post Office, Facebook, Dominos, Walmart, Yahoo... and the list goes on and on.
We all have heard the lectures of good passwords and bemoan all those password character requirements, but ultimately, it will keep your online profiles safer. Even strongly encrypted passwords can find themselves vulnerable to brute force password guessing.
Lastly, so many people have confessed to me they use the same password for everything. If you look at the list of compromised servers, you can imagine how this practice can magnify your risks of identity theft.
Heartbleed
 As Heartbleed has been making waves in the news and through-out the Internet community, we'd like to inform our users that our servers are not, nor ever were vulnerable to the attack.
As Heartbleed has been making waves in the news and through-out the Internet community, we'd like to inform our users that our servers are not, nor ever were vulnerable to the attack.
For more information on the exploit, visit http://heartbleed.com/
New Ransomware Virus Spreading
A new threat has emerged that is being called "Bad Rabbit"
This is a variant of other viruses that disable a user's computer by encrypting all the files.
More information is available by googling "Bad Rabbit" but the main thing to keep in mind is that this virus poses as an Adobe Update.
Avoid clicking on any adobe updates in the mean time.
Farewell AltaVista
 Before Google there were few search engines that stood above its peers. Alta Vista was one such.
Before Google there were few search engines that stood above its peers. Alta Vista was one such.
In 1995 it was a forerunner in websearch technology. It was one of the first search engines to offer online translations through its Babelfish.
Since the rise of Google, the once mighty search engine has become nearly forgotten. With the advent of Google, many users were lured away and AltaVista declined. By 2001 Google overtook AltaVisa in number of searches. Some believe its troubles started 1998 when AltaVista went through a long line of owners, each changing the product little. In 2003 MSN was competing for the acquisition of AltaVista against Overture. Overture won its bid, but in turn was acquired by Yahoo!
Now, Yahoo! has decided (again) to put an end to the Internet legend once and for all. It has announced that starting July 8, 2013, AltvaVista.com will just recommend searchers to use Yahoo! instead.